Google Cloud Armor customers were hit by a distributed denial of service (DDoS) directed at the HTTPS protocol. It reached 46 million requests per second (RPS), making this the most significant attack of its kind.
The attack escalated quickly from 100,000 RPS to 46 million RPS in just 2 minutes. This is almost 80% more than Cloudflare had previously recorded for an HTTPS DDoS of 26 million RPS.
The attack began at 09:45 Pacific Time on June 1st and was initially limited to 10,000 RPS.
The attack reached 46 million requests per second just two minutes later. Google claims that the attack peaked at 46 million requests per second. This is equivalent to obtaining all daily Wikipedia requests in 10 seconds.
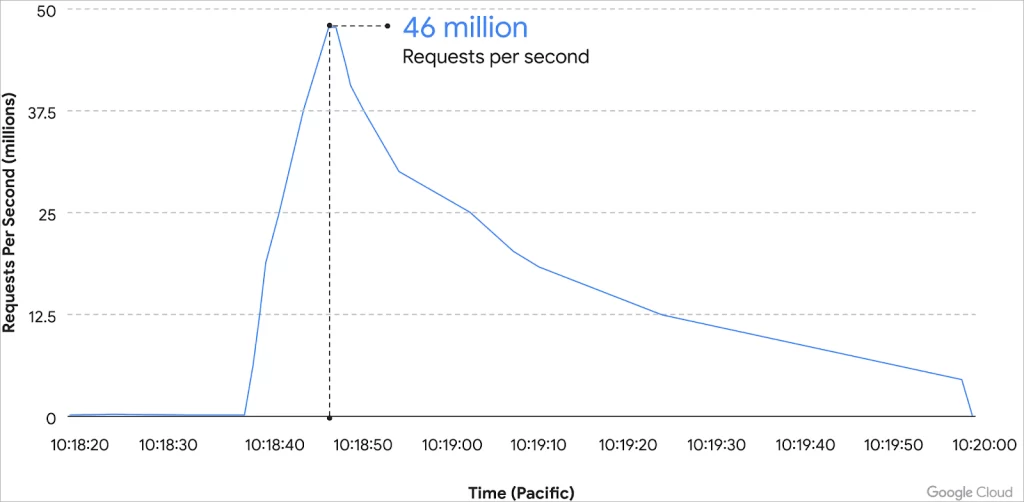
Fortunately, The customer had already deployed Cloud Armor’s recommended rule, allowing operations to continue. The assault was over in 69 minutes.
“Presumably, the attacker likely determined they were not having the desired impact while incurring significant expenses to execute the attack,” reads a report from Google’s Emil Kiner (Senior Product Manager) and Satya Konduru (Technical Lead).
Although the malware responsible for the attack is still unknown, the geographical distribution of the services used suggests that it was Meris.
This botnet is responsible for DDoS attacks with peaks at 17.2million RPS and 21.8million RPS, both records at the time.
Meris is well-known for using unsecure proxy servers to send horrible traffic to conceal the source of the attack.
Google researchers found that attack traffic originated from only 5,256 IP addresses in 132 countries. They leveraged encrypted requests (HTTPS) to indicate that the devices that sent the requests had powerful computing resources.
Another characteristic of the attack is the use of Tor exit nodes to deliver the traffic. They were responsible for only 3% of attack traffic and 22% (1169) of the sources who channelled their requests through Tor.
Related Popular Stories:
