The Jenkins security team disclosed 34 vulnerabilities in 29 plugins of the Jenkins open-source automation server. 29 of these bugs were zero days and are still being fixed.
Jenkins is an extremely popular platform with support for over 1,700 plugins. It’s used worldwide by enterprises for developing, testing and deploying software.
According to Jenkins, the zero-day CVSS base scores range in severity from low to high. The impacted plugins have more than 22,000 installations.
The full list of flaws still to be fixed includes XSS and Stored XSS bugs, Cross-Site Request Forgery Bugs (CSRF), missing or incorrect permission checks, passwords, secrets API keys, tokens stored in plain text, and passwords, secret messages, as well as usernames, passwords, keys, API keys, and other vulnerabilities.
Most of the most dangerous zero-days require user interaction to be exploited by remote attackers with low privileges in low complexity attacks.
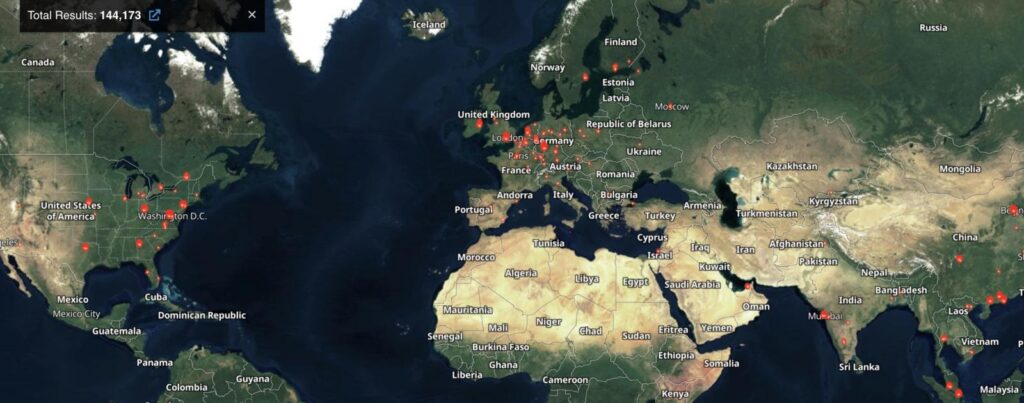
Shodan data shows that more than 144,000 Jenkins servers are currently exposed to the Internet. These Jenkins servers could be vulnerable to attacks if they use an unpatched plugin.
Although the Jenkins team has already patched four plugins (i.e. GitLab, requests, plugin, TestNG Results and XebiaLabs XL release), many are still vulnerable. The list is shown below:
- GitLab Plugin up to and including 1.5.34
- HPE Network Virtualization Plugin up to and including 1.0
- Jigomerge Plugin up to and including 0.9
- Skype notifier Plugin up to and including 1.1.0
- TestNG Results Plugin up to and including 554.va4a552116332
- Validating Email Parameter Plugin up to and including 1.10
- Matrix Reloaded Plugin up to and including 1.1.3
- Build Notifications Plugin up to and including 1.5.0
- build-metrics Plugin up to and including 1.3
- Cisco Spark Plugin up to and including 1.1.1
- Deployment Dashboard Plugin up to and including 1.0.10
- Elasticsearch Query Plugin up to and including 1.2
- eXtreme Feedback Panel Plugin up to and including 2.0.1
- Failed Job Deactivator Plugin up to and including 1.2.1
- OpsGenie Plugin up to and including 1.9
- Plot Plugin up to and including 2.1.10
- Project Inheritance Plugin up to and including 21.04.03
- Recipe Plugin up to and including 1.2
- Request Rename Or Delete Plugin up to and including 1.1.0
- requests-plugin Plugin up to and including 2.2.16
- Rich Text Publisher Plugin up to and including 1.4
- RocketChat Notifier Plugin up to and including 1.5.2
- RQM Plugin up to and including 2.8
- XebiaLabs XL Release Plugin up to and including 22.0.0
- XPath Configuration Viewer Plugin up to and including 1.1.1
“As of publication of this advisory, there is no fix,” the Jenkins security team said when describing the unpatched vulnerabilities.
Although none of these vulnerabilities is considered critical, they could allow threat actors to remotely execute code on vulnerable servers to take control. They could also be used as a weapon against enterprise networks.
It wouldn’t be the first such incident since unpatched Jenkins servers were compromised to mine Monero cryptocurrency.
Potential attackers will more likely use these zero days for reconnaissance attacks that allow them to gain greater insight into the infrastructure of a target company.
You May Like These Stories:
